How B2B Tech Companies Should Manage Domain Assets
-
Last Updated:
31 Mar 2026
-
Read Time:
11 Min Read
-
Written By:
 Isha Choksi
Isha Choksi
-
381
Table of Contents
Effective domain asset management helps B2B organizations secure DNS infrastructure, prevent subdomain attacks, and streamline governance while supporting M&A, vendor evaluation, and operational continuity across complex digital environments.
Why Domain Assets Belong in Your Risk Register
In the world of enterprise IT governance, infrastructure risk assessments are commonly performed on cloud architecture, SaaS dependencies on third-party providers, and the integrity of the data pipelines that facilitate business processes. However, the infrastructure of domain registrations, DNS configurations, and the overall ecosystem of subdomains that underlie every aspect of a business's online presence is not commonly considered in the same way. This is a foundational problem that has a number of consequences.
The first step in remedying the problem of domain infrastructure in enterprise governance involves a common but often overlooked aspect: what you actually own and who owns it. Prior to the establishment of a governance framework, it is essential that stakeholders understand the state of their domain registrations. This information may be obtained through a domain registration lookup, which provides information on the registrations themselves, the registration dates, the registrar, and the nameservers used in the configuration. For companies that have expanded through acquisition or allowed domain registrations to be managed by different business units, even the most rudimentary step in the process may reveal significant discrepancies in assumed ownership and actual ownership.
The scope of the article is with regard to the operational, security, and strategic aspects of domain asset management for the mid-market and enterprise B2B technology segment. It is divided into four domains of concern: governance architecture, security operations, M&A and transition risk, and vendor infrastructure evaluation.
Domain Security: The Subdomain Attack Surface
Subdomain Takeover: Mechanism and Prevalence
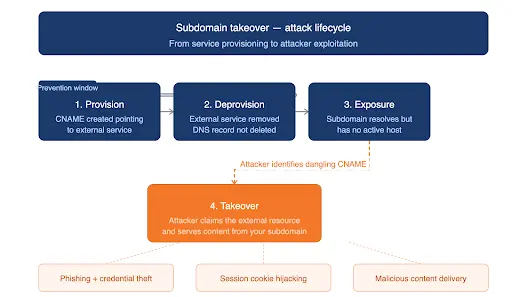
This is a well-known vulnerability class and has been documented in detail. It is located at the intersection of DNS misconfiguration and external services lifecycle management. It works like this: If an organization wants to use an external service and provisions a subdomain using a CNAME record pointing to the external service — a cloud hosting platform or a marketing platform, and then later deprovisions the external service without removing the DNS record, the CNAME becomes a dangling record. If an attacker then claims the external service, they can serve content out of the subdomain without any authentication.
The OWASP Web Security Testing Guide has formally classified subdomain takeover testing in the OWASP Web Testing Guide in section 4.2.10 of the Configuration and Deployment Management Testing framework. This is because subdomain takeover is such a common vulnerability in enterprise environments. If an attacker is able to subdomain takeover an organization's domain, they can then use the domain to serve malicious content, engage in phishing attacks, and capture session cookies for the parent domain.
It is also worth noting that the vulnerability is not limited to the CNAME record. This is further confirmed by the OWASP documentation, which indicates that the subdomain takeover vulnerability can be exploited using various DNS record types such as A, MX, NS, and TXT records. It is further indicated that the takeover of the NS record has the greatest potential for damage in the event of a successful attack, as it would result in the full control of the DNS zone.
 ?
?
Governance-Level Prevention
Preventing subdomain takeover is not a technical problem; it is an operational problem. Organizations that deprovision their virtual hosts and cloud-based infrastructure before deprovisioning their DNS records leave a window of vulnerability that can be open for an indeterminate period of time. The policy change to correct this is not ambiguous: deprovision DNS records before deprovisioning external resources.
To implement this policy change, organizations need to coordinate across functional teams. Those teams responsible for cloud-based resource deprovisioning and development teams need a defined process to deprovision cloud-based resources. That process needs to be formalized and not rely on ad hoc communication.
Finally, organizations need to have a comprehensive list of their subdomains and need to automate tools that identify dangling CNAMEs. Subdomain visibility is a critical component of an enterprise’s security operations. Organizations need to include tools that identify subdomains and identify external resource records in their standard security operations chain. In addition to their utility in preventing subdomain takeover, DNS query logs can be a high-fidelity indicator of command and control activity, data exfiltration activity, and lateral movement within an enterprise network.
Domain Due Diligence in M&A and Technology Transitions
The Acquisition Integration Gap
Mergers and acquisitions create predictable domain governance challenges that are frequently underestimated during due diligence. Two organizations with independently managed domain portfolios bring together different registrars, different administrative contacts, different DNS infrastructure providers, and often different levels of documentation. Integration timelines expand when these discrepancies surface post-close rather than during the diligence process.
Effective pre-acquisition domain due diligence should address five areas:
- Portfolio completeness: Is there a comprehensive inventory of all registered domains, including those held by subsidiaries and acquired entities? Are renewal dates current, and are there any domains that have lapsed and may represent former digital assets now held by third parties?
- Subdomain security posture: Are there dangling CNAME records or other misconfigured DNS entries in the target's environment? These become part of the acquirer's attack surface on day one of the deal close.
- Trademark alignment: Do the target's domain holdings align with their registered trademarks and brand assets? Are there third-party registrations of brand-adjacent domains that could create post-acquisition legal exposure under the UDRP or applicable trademark law?
- DNS infrastructure dependencies: Is DNS managed internally or through a third-party provider? What are the contractual SLA terms and the technical characteristics of that provider's infrastructure, including DNSSEC support and anycast coverage?
- Registrar transfer readiness: What are the transfer policies and associated timelines for the target's registrar? Standard inter-registrar transfers for generic TLDs such as .com and .net typically complete within five to seven business days under normal conditions, but administrative holds, transfer locks, or unresolved disputes can extend that timeline significantly — creating integration delays that compound other post-close operational pressures.
Technology Transition Risk: Email and DNS Continuity
Outside of M&A, domain and DNS risk is often caused by technology transitions that organizations do not typically think of as infrastructure changes. For instance, a move from one marketing automation system to another, a change in email service provider, or a move from agency-managed digital presence to in-house staff all require changes in the domain namespace that, when incorrectly configured, can cause issues in email delivery, invalidate SSL certificates, and negatively impact dependent systems.
Email delivery is a sensitive area that is impacted by the incorrect configuration of DNS. SPF, DKIM, and DMARC are all email authentication systems that depend on DNS, and an incorrect configuration during a platform transition can harm a previously built email reputation that took years to develop. Enterprise email systems that enforce strict DMARC policies may reject email from domains that are incorrectly configured, causing issues in email delivery and creating reputational risk for enterprises.
In order to mitigate transition risk, a comprehensive DNS record inventory, including all TXT records, MX configurations, CNAME chains, and TTL values, needs to be maintained prior to executing any platform change. This needs to be considered a formal change management activity rather than an afterthought in operations.
Domain Valuation: A Framework for Asset Decision-Making
Why Valuation Matters for Technology Companies
Domain assets have a financial value that is seldom captured in the enterprise’s balance sheet. For organizations that are fundraising, considering M&A activity, or changing their brand name, these intangible domain assets create a gap in the information provided to investors and buyers. A new investor or acquirer that is unaware of these domain assets will most likely assume a worst-case scenario for these intangible assets and will be more likely to lower their valuation offers or create friction in a potential acquisition.
The valuation of domain names is also operationally relevant in deciding whether to acquire a new domain name that complements an existing brand, whether to sell a non-core domain name, and whether to defensively acquire a new domain name that is adjacent to an existing brand to prevent a competitor or a domain squatter from doing so.
Key Valuation Factors
Domain value is determined by a combination of factors, each of which can be assessed independently and weighted according to organizational context:
- Top-level domain (TLD): The .com TLD remains to hold the highest level of trust for enterprises, and in a market where short .com domains are increasingly hard to find. Industry-related TLDs such as .io and .ai vary in recognition depending on the segment of buyers. .io is well recognized in developer-related markets, whereas .ai is increasingly linked to machine learning and artificial intelligence-related product types.
- Domain length and composition: Short, pronounceable domains in premium TLDs command significant secondary market premiums. Dictionary words and common two-word combinations are consistently more valuable than constructed or coined terms.
- Keyword relevance: Domains containing high-intent commercial keywords aligned with a product category carry demonstrable brand recognition value and potential organic search benefit. This factor is particularly material in competitive B2B software categories where organic acquisition is a meaningful channel.
- Registration age and backlink equity: Domains with established registration histories and inbound link profiles from authoritative sources have accumulated authority that cannot be quickly replicated. This is a non-trivial asset in markets where search visibility drives the enterprise pipeline.
- Historical traffic: Domains with documented traffic history carry additional value as operational assets rather than speculative registrations. Third-party traffic estimation tools and web archive data provide reference points for substantiating these claims during M&A or fundraising discussions.
Evaluating DNS Infrastructure and Domain Registrar Vendors
Infrastructure-Grade Vendor Criteria
DNS infrastructure is as operationally critical as database or compute infrastructure. Outages or latency at the DNS layer affect every service that depends on domain resolution — which, for most organizations, means all of them. Vendor evaluation should reflect this criticality rather than defaulting to cost as the primary selection criterion.
The evaluation framework for DNS and registrar vendors should cover the following dimensions:
Reliability and SLA structure: What is the provider's documented uptime history for authoritative DNS? What are the contractual SLA terms, and what remedies exist for SLA breaches? Providers that do not publish uptime history or that offer only best-effort commitments represent meaningful operational risk for enterprise deployments.
Security capabilities: DNSSEC support, two-factor authentication enforcement for registrar account access, role-based access controls, and audit logging are baseline requirements for enterprise-grade domain management. The absence of any of these capabilities should be a disqualifying factor in vendor selection, not a negotiating point.
Anycast network coverage: Authoritative DNS performance depends on the geographic distribution of the provider's anycast network. For organizations with global user bases or enterprise customers across multiple regions, DNS resolution latency is a real operational variable with direct impact on application performance and user experience.
Portfolio management tooling: For organizations managing more than a small number of domains, the quality of management tooling determines whether governance is operationally sustainable. Bulk management capabilities, automated renewal workflows, audit export functionality, and API access for integration with IT Asset Management (ITAM) systems distinguish enterprise-grade providers from consumer-oriented registrars.
Transfer and exit provisions: Vendor lock-in is a genuine risk in domain management. Registrars that impose transfer restrictions, extended waiting periods, or administrative friction on portfolio migrations create operational dependency that may not be apparent during onboarding. Transfer policies, associated timelines, and bulk transfer capabilities should be evaluated explicitly before committing a large portfolio to any single provider. The ease of exit is as important as the quality of onboarding.
Integration with ITAM and Security Operations
Domain management is, of course, far from being a standalone activity from the rest of the IT infrastructure. At leading organizations, domain and DNS-related assets are integrated into the overall IT Asset Management infrastructure, including software, hardware, and SaaS assets. This gives a single, integrated view of digital assets that is valuable for both operational governance and security operations.
For security operations, query log data from the DNS is a high-fidelity indicator for several types of security events. For example, unusual patterns of DNS query activity can be indicative of command and control activity from compromised endpoints. An unusual spike in NXDOMAIN responses can be indicative of malware beaconing or domain generation algorithms. Changes in authoritative nameserver configuration can be indicative of domain hijacking. These indicators are only valuable, however, when they can be acted on, and this requires that both the tools and organizational structures be in place to leverage this information.
Building a Domain Governance Program: Operational Framework
A domain governance program for a mid-market to enterprise B2B technology company should be structured around five operational pillars:
- Complete inventory and centralization: Enumerate every domain across all registrars, business units, and acquired entities. Migrate to a single enterprise registrar with unified billing and access controls. Assign a primary administrative contact and a designated secondary for every domain in the portfolio.
- Ownership and accountability assignment: Every domain should have a named business owner responsible for renewal decisions, configuration changes, and annual retention justification. Domains without a documented owner and a current business purpose should enter a disposition review — either transferred to the appropriate owner or scheduled for de-registration. Without individual accountability, governance frameworks fail at the operational level regardless of how well they are designed.
- Subdomain visibility and security integration: Maintain a continuously updated subdomain inventory. Integrate subdomain enumeration into security operations workflows. Establish and enforce the operational sequencing rule without exception: DNS record removal must precede virtual host deprovisioning. This single procedural control eliminates the primary condition that enables subdomain takeover attacks.
- Defensive registration policy: Define and execute a defensive registration policy covering brand-adjacent TLDs, common misspellings, and domain variants associated with high-value product or brand names. The cost of defensive registrations is consistently lower than the cost of recovering domains through UDRP proceedings or litigation, and substantially lower than the brand and trust damage that can result from an adversarially held brand-adjacent domain.
- Valuation and financial documentation: Maintain current valuation estimates for primary and strategically significant domains. Update these estimates when material business events occur — funding rounds, acquisitions, rebrands, or significant changes in organic search performance. Ensure that domain assets are reflected accurately in financial reporting and disclosed appropriately in M&A and investor contexts.
Conclusion: Domain Infrastructure as a Strategic Asset Class
The risks in the domain infrastructure space in terms of operations and security are well understood, but the strategic aspect is equally significant. For B2B tech companies, domain infrastructure is the basis for brand trust, search engine visibility, email deliverability, and API reliability. Domain infrastructure is also a hard asset, one whose value is quantifiable but typically not quantified, and therefore not protected.
The governance gap in domain infrastructure management is not a technology problem. The solution stack to address it is available today. It is an organizational problem: a business process that sits at the nexus of IT operations, security, legal, and finance, which in most companies gets partial attention from each group individually, but no attention from all groups collectively.
This is a problem that requires sponsorship, ownership, and a governance framework that analyzes domain infrastructure in the same way it analyzes software licensing, cloud services, and intellectual property. Companies that solve this problem are better positioned for M&A activity, DNS-layer security threats, and brand protection cases. Companies that don’t will continue to incur the rising costs of domain infrastructure debt, most visibly when the company can least afford it.
Recent Blogs
How to Choose an AI Workflow Automation Platform for Enterprise Operations
-
25 May 2026
-
6 Min
-
53
A Beginner’s Guide to Creating Apps Without the Usual Complexity
-
13 May 2026
-
8 Min
-
200